Debit card fraud without using your card?

NEWNow you can listen to Fox News articles!
Every so often, we get an email that stops us cold. Not because it’s amazing. Not because it’s careless. Because it sounds impossible.
Sheri M. from Georgia recently wrote to us with this question:
“Yesterday I found out someone stole my debit card information. I was notified by my bank around 10:00 last night that someone tried to use my card in Brazil. I’m in the South of the United States and I’ve never traveled outside of the country. What I’m having trouble understanding is that this debit card has never been used and has never been out of an enclosure, and I didn’t lock it to work. So someone may have my card information, and after talking to several people, they are confused that what will they tell me?
A GHOST-TAPPING SCAM TARGETING USERS TO TAKE PAYMENT
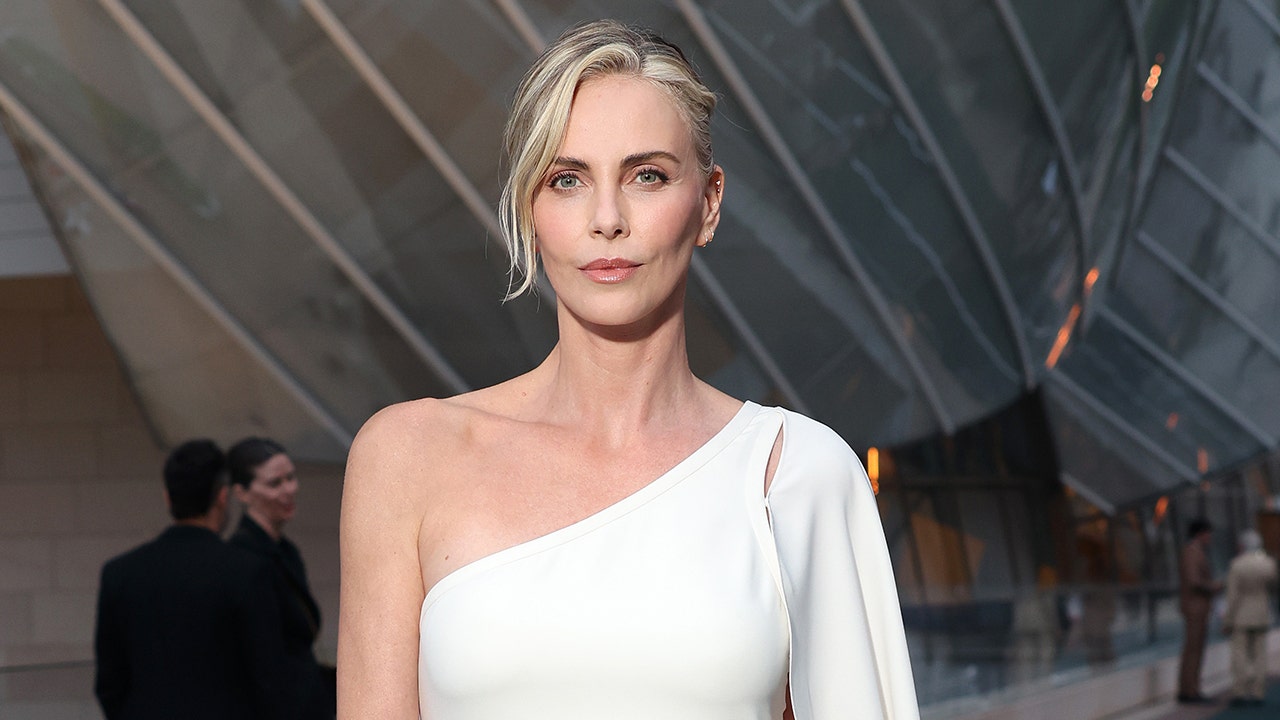
Debit card numbers can be digitally compromised through system breaches or automated number guessing attacks. (Fizkes/Getty Images)
Sheri, first of all, we are glad that your bank has contacted you. That warning tells you that fraud monitoring has worked. Now let’s talk about the part that sounds fake. How can one use a debit card that has never left a locked vault?
If you’ve asked that question, you’re not alone. This type of debit card fraud happens more often than most people realize. And it probably doesn’t involve someone physically touching your card.
Sign up for my FREE CyberGuy report
Get my best tech tips, emergency security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join CYBERGUY.COM newspaper.
How does debit card fraud happen without using the card
If the card is compromised without use, the problem is usually digital. Here are the most likely explanations.
1) The number is displayed before you receive it
Debit cards go through many systems before they reach your mailbox. Third-party vendors produce, code and deploy them. That means the card number is in the database long before you open the envelope. If one of those systems is breached, criminals can obtain card numbers in bulk. They do not need a physical card. They will never need your home. If so, it has nothing to do with your vault.
2) BIN attack may be responsible
Every debit card starts with a bank identification number. Hackers use the software to generate the remaining digits at high speed. They test thousands of combinations using small transactions or international approvals to see which numbers work. This is known as a BIN attack. They don’t steal your specific card. They guess numbers that are statistically valid. Once your card is activated, even if it has never been used, it becomes part of the pool that can be checked. A foreign effort, such as the one in Brazil, is often approved for testing. It feels personal. In fact, it’s automatic.
WEB SKIMMING ATTACKS HUNDREDS OF MAJOR PAYMENT NETWORKS

A customer completes a transaction at Pike Place Market in Seattle, Washington, on May 28, 2025. Financial security experts recommend canceling compromised cards and checking accounts immediately after a fraud alert. (M. Scott Brauer/Bloomberg via Getty Images)
3) Processor or network weak point
Sometimes the exposure does not come from the bank itself. A weak link can include:
- Payment processor
- Card network
- The backend of the digital wallet
- A service provider
Front-line bankers are often invisible to these system-level problems. Patterns can take time to appear within. That’s why you may not get a clear explanation right away.
4) Background programs provide numbers in advance
Most banks pre-assign card numbers or connect them to digital systems before you swipe the card. If that background data is revealed, the physical card that remains locked does not matter. This is why debit card fraud without using the card is still possible.
Why did the work appear abroad?
You may wonder why the effort came from Brazil. Foreign authorizations are often used as screening activities. Criminal groups use small or irregular area charges to determine which numbers work. Once the case is over, it grows. The good news is that your bank has blocked it.
What you should do right now
If this happens to you, take immediate action.
- Cancel the card completely. Just don’t lock it. Make sure the number is blocked permanently.
- Request a new card number. Make sure it is not a reissue of the same digits.
- Monitor your checking account daily for at least 30 days.
- Check your credit with all three credit bureaus.
- Add identity monitoring to detect widespread abuse.
That last step is often overlooked.
WHY DO THEY OPEN BANK ACCOUNTS IN YOUR NAME

Experts say debit card fraud often happens without the physical card being used or stolen. (Nikos Pekiaridis/NurPhoto via Getty Images)
Why is it important to guard your identity
Debit card fraud can be classified. It may also indicate greater data exposure.
If your card number is exposed through a breach or merchant leak, other personal information may be compromised as well. Email addresses, phone numbers and Social Security numbers often appear together in stolen datasets. This is where early detection becomes critical.
Our top recommendation for Identity Theft Protection monitors credit activity, financial accounts and the web’s black markets for signs that your identity is being misused. You get instant alerts so you can respond before small incidents turn into big problems.
Instead of waiting for a late night fraud alert, you get early detection.
See my best tips and picks Best Identity Theft Protection of Cyberguy.com.
Ways to stay safe from invisible debit card fraud
You cannot control global criminal networks. You can reduce your exposure.
- Keep debit cards locked in your banking app when not in use
- Turn on real-time transaction alerts
- Use credit cards to shop online whenever possible
- Freeze your credit as a preventative measure
- Avoid storing debit card information on all merchant sites
- Use identity monitoring for more protection
Layered security gives you more control.
Kurt’s priority is taking
Sheri’s experience feels impossible because she did everything right. The card never came out of the vault. It was never used. No one had access. However, the price was still being assessed around the world. That is the reality of today’s financial crime. It is automated, remote and program driven.
If this can happen on a card locked in a vault, what does that say about how safe our financial system really is? Let us know by writing to us at Cyberguy.com.
CLICK HERE TO DOWNLOAD THE FOX NEWS PROGRAM
Sign up for my FREE CyberGuy report
Get my best tech tips, emergency security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join CYBERGUY.COM newspaper.
Copyright 2026 CyberGuy.com. All rights reserved.